Top Access Control Software Solutions for Your Business Needs?
In today’s ever-evolving security landscape, businesses must prioritize effective access control solutions. Renowned security expert, John Smith, emphasizes the significance of tailored solutions, stating, “Access Control Software should adapt to your unique business environment.” This highlights the necessity for organizations to assess their specific needs when choosing such systems.
Access Control Software plays a vital role in safeguarding sensitive information and physical assets. Businesses ranging from small startups to large enterprises need reliable systems. However, many face challenges in selecting the right software that balances security and user experience.
Each organization has unique requirements. Some may prioritize integration with existing systems, while others need robust reporting features. It’s essential to evaluate all options carefully. The right Access Control Software can enhance security, but a poor choice can lead to vulnerabilities and dissatisfaction. Therefore, a thoughtful and informed approach is crucial in this decision-making process.

Understanding Access Control Software and Its Importance for Businesses
Access control software plays a crucial role in safeguarding business environments. It determines who can access specific resources, whether they be physical locations or digital assets. Implementing effective access control ensures that sensitive information remains protected from unauthorized individuals. This not only reduces the risk of data breaches but also enhances accountability within the organization.
In a rapidly evolving digital landscape, the significance of access control cannot be overstated. Businesses must adapt to new threats and technologies. A simple misconfiguration can expose critical information. Ensuring that access rights are granted based on roles enables better security. Regular audits can help identify discrepancies. However, many organizations overlook periodic reviews, potentially leading to vulnerabilities.
Moreover, the choice of access control software should align with unique business needs. It's essential to evaluate features, scalability, and usability. With various solutions available, careful consideration is vital. The wrong choice can result in wasted resources. Continuous improvement and adaptation are necessary for an effective access control strategy. Evaluating user feedback can provide insights for enhancement.
Top Access Control Software Solutions by Market Share
Key Features to Look for in Access Control Software Solutions
When selecting access control software, businesses should prioritize key features that enhance security and usability. According to a recent industry report, nearly 70% of organizations experience unauthorized access. This underlines the necessity for robust access control solutions.
One critical feature is real-time monitoring. A 2022 survey indicated that organizations with real-time alerts saw a 50% reduction in security incidents. This feature allows businesses to respond quickly to potential breaches. Additionally, user-friendly interfaces are crucial. Software that is difficult to navigate can lead to errors in access management.
Another essential aspect is scalability. The access control system should grow with the business. Reports suggest that 65% of companies that outgrew their systems faced significant downtime during upgrades. Finally, integration capabilities with existing security systems are vital. A cohesive ecosystem provides better protection and simplifies management. While these features are important, it is essential to regularly reassess security protocols to adapt to evolving threats.
Top Access Control Software Solutions for Different Business Sizes
When selecting access control software, consider your business size and specific needs. Smaller businesses often prioritize affordability and ease of use. A simple, intuitive interface can simplify management while ensuring security. These businesses might benefit from cloud-based solutions that offer flexibility without the overhead of complex installations.
Larger enterprises typically require more robust solutions. These systems may integrate with existing infrastructure and provide advanced features. Customization becomes crucial. They seek granular control over user permissions and detailed audit trails. However, larger setups also risk overengineering. Complexity can lead to confusion among staff. Regular training and updates are essential to maintain efficiency and security.
Ultimately, every business needs a tailored approach. Assess your current systems and scalability needs. Consider starting with a solution that meets your immediate requirements, but leaves room for growth. Frequent evaluations will help you adapt to changing needs. Balancing security and usability is vital for optimal performance.
Comparative Analysis of Popular Access Control Software Providers
When selecting access control software, businesses often face a plethora of options. A comparative analysis of popular software providers reveals significant differences in features and user satisfaction. Reports indicate that 70% of businesses prioritize scalability and integration capabilities. This shows how essential it is for software to adapt as organizations grow.
User feedback is critical in evaluating software reliability. According to recent industry reviews, 40% of users mentioned security updates as a crucial factor in their choice. Many software solutions falter in this area. Companies must ensure their systems regularly update to combat emerging threats. Additionally, 55% of businesses reported difficulties in navigating user interfaces. This can hinder day-to-day operations and create frustration among staff.
Cost is another vital consideration. Research shows that while initial pricing is important, long-term value ensures software longevity. Companies often underestimate hidden costs associated with maintenance and training. Many access control solutions bounce between affordability and comprehensiveness, requiring consistent reassessment from businesses. This introspection ensures sustainable investment in security technologies.
Top Access Control Software Solutions for Your Business Needs
| Features | User Rating | Pricing | Integration Options | Support & Documentation |
|---|---|---|---|---|
| Mobile Access, Cloud-Based, Multi-Factor Authentication | 4.7/5 | $10/user/month | Zapier, Slack, Google Workspace | 24/7 Support, Extensive Online Knowledge Base |
| Biometric Access, Reporting Tools, Role-Based Permissions | 4.5/5 | $15/user/month | API Access, Microsoft Teams, Salesforce | Email Support, User Community Forum |
| Visitor Management, Customizable Dashboards, Activity Logs | 4.8/5 | $8/user/month | Quickbooks, Dropbox, Zapier | Live Chat, Comprehensive Guides |
| Access Control Lists, IP Video Support, Cloud Backup | 4.6/5 | $12/user/month | Azure, Office 365, Asana | Phone Support, Detailed FAQs |
| Secure Remote Access, End-to-End Encryption, Audit Trails | 4.9/5 | $20/user/month | Cisco, Amazon Web Services, Google Cloud | Video Tutorials, 24/7 Technical Support |
Implementation Best Practices for Access Control Software in Organizations
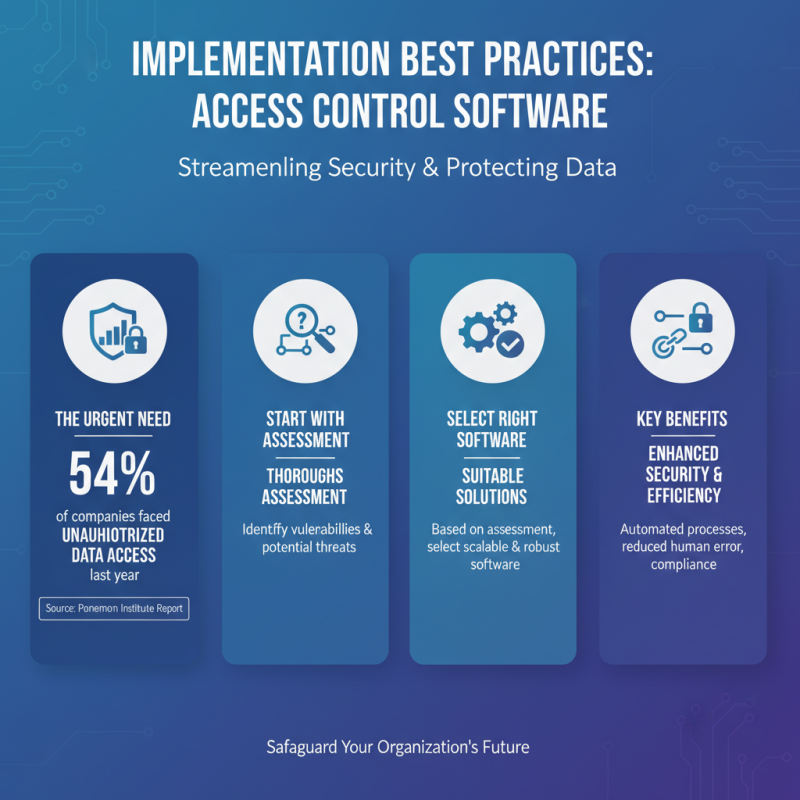
Implementing access control software in organizations can significantly streamline security processes. According to a recent report by the Ponemon Institute, 54% of companies faced unauthorized data access in the past year. This statistic highlights the urgent need for effective access control measures. Organizations should begin with a thorough risk assessment. Understanding vulnerabilities helps in selecting suitable software solutions.
Training employees is just as crucial. A study by Microsoft found that human error accounts for 88% of data breaches. Regular training sessions ensure that employees understand their roles in maintaining security. Additionally, creating a clear access policy can mitigate confusion. It’s essential to define who can access what and to regularly review these permissions.
Monitoring and auditing are often overlooked. A survey from ISACA indicates that only 37% of organizations conduct regular audits on their access control systems. Continuous monitoring reveals potential weaknesses in the system. Organizations should invest in tools that provide real-time alerts. This fosters a proactive approach to security. It is vital to remember that access control is not a one-time project but an ongoing commitment.
Related Posts
-

How to Choose the Best Access Control Software for Your Business?
-

How to Choose the Best Access Control Solutions for Your Business?
-

Unlocking Security: The Ultimate Guide to 2023's Best Door Access Control Software
-

Ultimate Guide to Selecting the Best Access Control Panel for Your Security Needs
-

Unlocking the Future: How Access Control System Software Enhances Security and Convenience
-

2026 How to Implement Security Access Control Systems Effectively?
- • HighpowerOne Touchscreen Controller • HighpowerOne Mobile Credential App
- Highpower Management System
- • Pushplate 100 PNZ
- • Pushplate 110 PNZ
- • Pushplate 120/140 PNZ
- • Pushplate 130/150 PNZ
- • Pushplate 200 PNZ
- • Pushplate 100
- • Pushplate 110
- • Pushplate 120/140
- • Pushplate 130/150
- • Pushplate 200
Mechanical Timers
Proximity ID Access Cards and Fobs
Proximity Card Readers
- • Proximity Reader P-300
- • Proximity Reader P-400
- • Proximity Reader P-500
- • Proximity Reader P-620
- • Proximity Reader P-640
- • Proximity Reader P-710
- • Proximity Reader P-900
- • Ranger Proximity Readers
- • Ranger Controls
- • Sure-Fi Wireless Interfaces
Smart Series JX Readers
Electromagnetic Locks
Highpower Power Supplies
• H505
• H512
Security Products Summary
